Introduction to NoSQL Injection Attacks
NoSQL injection attacks are a form of cyberattack where malicious users exploit vulnerabilities in NoSQL database systems to gain unauthorized access to, or manipulate, sensitive data. Just like SQL injection attacks, NoSQL injections pose a serious threat to application security. In this article, we'll discuss how to safeguard against NoSQL injection attacks in Node.js Express applications that use MongoDB, one of the most popular NoSQL databases.
Understanding the Basics of NoSQL Injection Attacks
NoSQL vs. SQL Injection
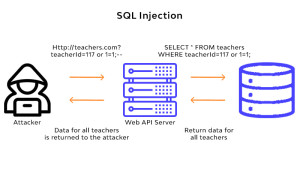
While both SQL and NoSQL injections target the database layer of an application, they differ in their approach. SQL injections exploit vulnerabilities in SQL queries, manipulating data by injecting malicious SQL code. NoSQL injections, on the other hand, exploit vulnerabilities in the NoSQL query language, which is typically JavaScript Object Notation (JSON).
How NoSQL Injections Work
NoSQL injections take advantage of weakly-typed languages like JavaScript, where type coercion can occur. Attackers manipulate input data to change the structure of the query, bypassing security measures and gaining unauthorized access to sensitive information. For example, an attacker might supply an object instead of a string, causing a query to return unintended results.
Key Techniques to Prevent NoSQL Injection Attacks
1. Use Parameterized Queries
Parameterized queries help prevent NoSQL injections by separating the query structure from the data being supplied. This prevents attackers from modifying the structure of the query. For instance, when using the MongoDB Node.js driver, use the $eq operator to create a parameterized query:
const user = await User.findOne({ username: { $eq: req.body.username } });
2. Implement Input Validation
Input validation ensures that data provided by users matches the expected format and type. Use libraries like Joi or Validator.js to validate user input:
const Joi = require("joi");
const schema = Joi.object({
username: Joi.string().alphanum().min(3).max(30).required(),
password: Joi.string().pattern(new RegExp("^[a-zA-Z0-9]{8,}$")).required(),
});
const validationResult = schema.validate(req.body);
if (validationResult.error) {
return res.status(400).send(validationResult.error.details[0].message);
}
3. Use Secure Defaults
Ensure that your application uses secure defaults, such as strict mode in JavaScript and safe write operations in MongoDB. For example, use the useNewUrlParser, useUnifiedTopology, and useCreateIndex options when connecting to MongoDB:
mongoose.connect("mongodb://localhost/mydb", {
useNewUrlParser: true,
useUnifiedTopology: true,
useCreateIndex: true,
});
4. Limit the Use of JavaScript Functions
Avoid using JavaScript functions, such aseval(), mapReduce(), and where(), which can expose your application to NoSQL injection attacks. Limit the use of these functions and, whenever possible, opt for safer alternatives like aggregation pipelines.
5. Regularly Update Dependencies
Keep your application's dependencies up-to-date to ensure you have the latest security patches. Use tools like npm audit to identify and fix vulnerabilities in your packages.
Implementing a Secure Node.js Express Application
To demonstrate a secure Node.js Express application that's protected against NoSQL injection attacks, we'll create a simple login route:
const express = require("express");
const mongoose = require("mongoose");
const Joi = require("joi");
const User = require("./models/user");
const app = express();
app.use(express.json());
mongoose.connect("mongodb://localhost/mydb", {
useNewUrlParser: true,
useUnifiedTopology: true,
useCreateIndex: true,
});
const schema = Joi.object({
username: Joi.string().alphanum().min(3).max(30).required(),
password: Joi.string().pattern(new RegExp("^[a-zA-Z0-9]{8,}$")).required(),
});
app.post("/login", async (req, res) => {
const validationResult = schema.validate(req.body);
if (validationResult.error) {
return res.status(400).send(validationResult.error.details[0].message);
}
const user = await User.findOne({ username: { $eq: req.body.username } });
if (!user) {
return res.status(400).send("Invalid username or password.");
}
// Compare passwords using bcrypt or other secure password hashing library
// ...
res.send("Logged in successfully!");
});
app.listen(3000, () => {
console.log("Server listening on port 3000");
});
In this example, we have created a simple Node.js Express application with a /login route. We have used Joi for input validation and MongoDB's $eq operator for parameterized queries. This helps protect the application against NoSQL injection attacks.
Conclusion
Safeguarding your Node.js Express application against NoSQL injection attacks is crucial for maintaining security and ensuring the integrity of your data. By employing best practices such as using parameterized queries, input validation, secure defaults, limiting the use of JavaScript functions, and regularly updating dependencies, you can reduce the risk of NoSQL injection attacks and build a more secure application.
And Finally
As always, I hope you enjoyed this article and got something new. Thank you and see you in the next articles!
If you liked this article, please give me a like and subscribe to support me. Thank you. 😊